Hacking the OSCP
As information security professionals we are fortunate to have a vast landscape of learning opportunities - and with ongoing developments in technology, the chance to learn new things is likely to continue for many years into the future. That being said, one of the great challenges of working in our field is figuring out what to learn - and building healthy habits to nurture continuous learning as an investment in ourselves.
And while I do not anticipate leaving the DevSecOps space anytime soon, earlier this year my employer (GitHub) offered the chance to pursue my Offensive Security Certified Professional (OSCP) certification. I jumped at the opportunity both to expand my own skills, as well as to expand my world view of this vast and shifting industry. For years I have thought of the OSCP as the gold standard for security certifications, and I wanted to see if “I’ve still got it” when it comes to security testing.
In the process of getting back into hacking and learning penetration testing skills, I’ve dusted off several long-unused habits that I share with you below. I hope that these reminders and recommendations help you in your own learning pursuits.
Do the Reading
When pursuing the OSCP, I cannot stress enough the value of reading through the course materials provided in the PEN-200 documentation. At times it can feel like a slog to get through, but I’ve found that if I use the web interface to read sections at a time and take notes side-by-side, the concepts start to become meaningful and useful.
That said - I often have trouble paying attention for long periods of time in front of text on a computer screen; If I’m not actively practicing the things I’m reading and taking notes on, I tend to become restless. Later on I’ll talk about the exercises and labs, but I usually read, take notes, and practice in a single learning cycle. It helps with starting to build the habit of using the things I’m learning, and breaks down that mild feeling of anxiety I get when trying something new and unfamiliar. If you likewise struggle with doing the reading, give the process of “read, write, do” a chance.
Taking Notes
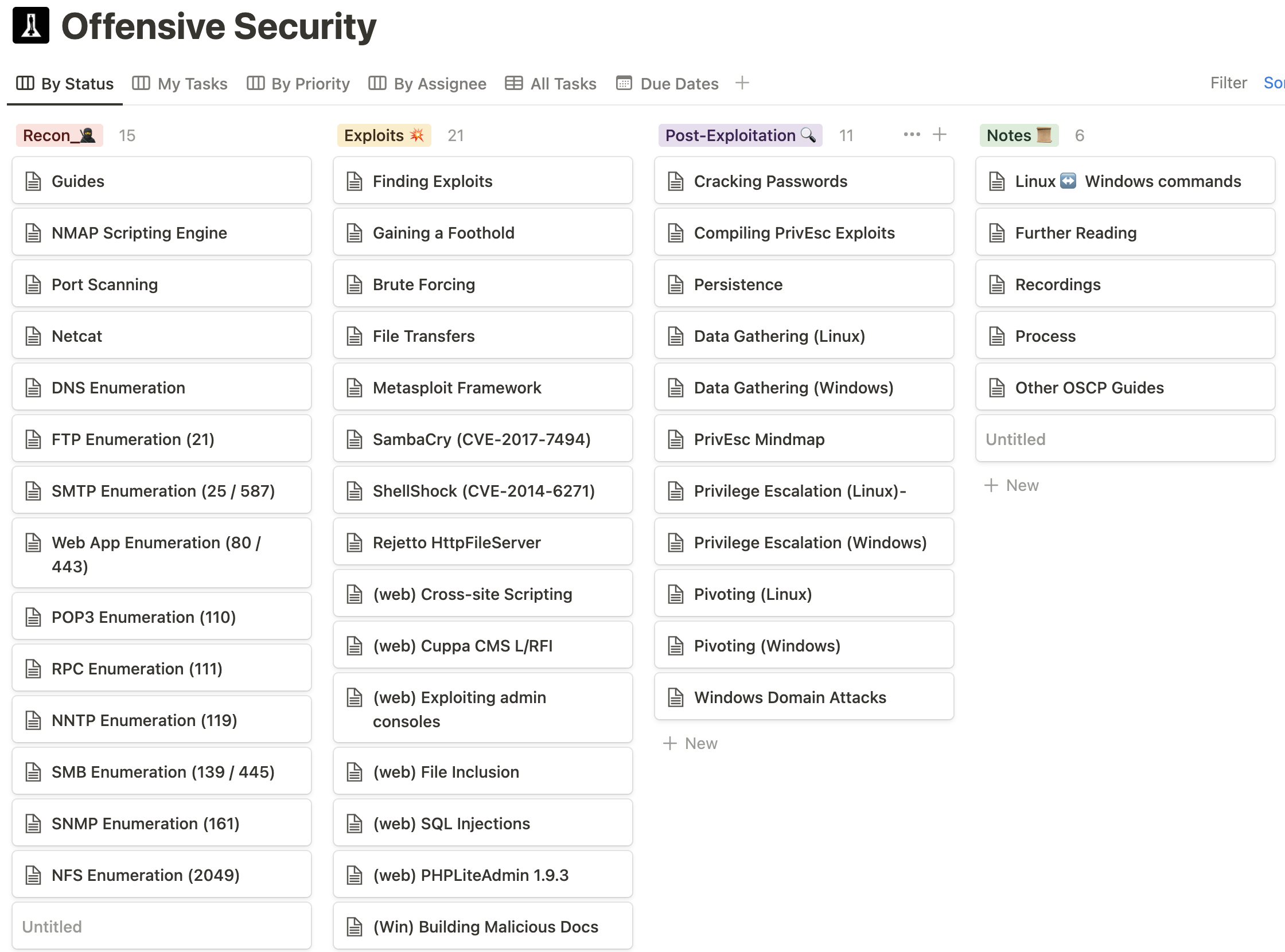
The act of writing something down is widely believed to help retain information as we learn. While I’m uncertain whether this carries over to typing out notes - one thing this process has helped me with is building a flow for my hacking process. The picture below is from the Notion board I’ve created for organizing what I’m learning and practicing. I work through my process from left to right as I practice in the labs, with each section containing code snippets and notes on various techniques.
Do the Exercises
While I much prefer practicing in the lab over working through the section exercises, what I’ve found is that the exercises make for a good primer as I refine my notes. This is also something I’ve found helps me get past that mild anxiety of trying out new techniques; if I’ve made all of my silly mistakes in the exercises - then doing it in the lab should be a lot easier. And if that’s not an incentive - by completing eighty percent of each section’s exercises (and rooting thirty lab machines) you get an extra ten bonus points on your exam!
Practice, Practice, Practice
It’s great to do the reading, take notes, and work through exercises - but none of that really matters until you actually start popping shells. Spending significant time in the labs to build-out a process and refine your notes will make all the difference when it comes to taking the exam. Through repetition and further exploration in the labs you turn knowledge into process; process into habit; and habit into instinct.
When you see things like SeImpersonatePrivilege Enabled on a Windows box for the first time you put in a significant amount of effort figuring out how to customize and refine privilege escalation exploits to get a system shell. By the fourth or fifth time you’ve seen it, you have a few tricks up your sleeve to quickly escalate privileges and pillage a box- all while looking for opportunities to move laterally into other systems.
Practice is the difference between wanting to be a 1337 H4x0r, and actually becoming one.
How to support this content: If you find this post useful, enjoyable, or influential (and have the coin to spare) - you can support the content I create via Patreon.️ Thank you to those who already support this blog! 😊 And now, back to that content you were enjoying! 🎉
Gathering Evidence (and more notes)
One of the greatest skills my good friend (and sensei) Jason Haddix taught me about performing security research was how to organize the information I’ve gathered about the target(s) I’m hacking into a mind map. This practice has helped me tremendously when organizing the information I know about a target in ways that unlock further opportunities for exploitation. It has also helped to refine my technique, and serves as a process I can fall back on when I am stuck.
As to specific mind mapping software, I’ve used both XMind and SimpleMind for performing web application bug bounty hunting on my MacBook. That said, I’ve recently been using Freeplane as I prepare for the OSCP - mostly because it’s cross platform, and is something that I can commit to a GitHub repository. I don’t love the fact that pasting line delimited rows of content ends up in a single node of a Freeplane mind map, but it works for my current purposes.
You are not Alone
If you’ve done the reading and the exercises, then there is absolutely no shame in seeking help. Thankfully the folks at Offensive Security have built a community on Discord that is both very welcoming and extremely helpful. When I find myself in a situation where I’ve exhausted all of my options, I usually start by searching for the IP address of the lab box I’m hacking. Being careful not to click on spoilers that might give too much away, I can usually find the help I need to proceed to get past the roadblock. If my search doesn’t provide what I need, I then try checking the forums before asking for help in the PEN-200 channels.
The most important thing to remember when asking for help is to make sure you take copious notes about what you learn from the process. You won’t be able to ask for help during your exam, so making sure you capture the information provided - and use it in practice until it becomes habitual - is a must. If you do this right, after a while you’ll find yourself asking for help less frequently - and eventually you’re the one providing help to others. Pay it forward!
Healthy Habits for Sustained Learning
Building a routine around studying - and allowing for down time to get adequate rest - are critically important to producing the results you’re striving for. For me this means spending at least 90 minutes working on the OSCP four nights a week, and a minimum four to six hours playing in the lab on weekends. That said, I don’t have children - and my wife appreciates the extra time to focus on writing her book. Do what is best for your own situation. Getting proper rest is important.
Likewise, if you’ve signed up for the Learn One (or Learn Unlimited) subscription - there’s absolutely no reason to rush through the content in order to take the exam. The point of earning the certification is to spend time learning, understanding, and practicing the content. Cramming is likely to be an altogether fruitless endeavor - costing you an exam attempt and having little to show for it.
In the end, the best investment you can make is in yourself. Sometimes that means pushing the pause button on work and learning new things - and that’s okay! Just remember that habits are hard to break - so don’t let yourself go too long without scheduling time to learn and practice new things. For my situation, I’ve managed to build in time to relax that includes watching anime while I enjoy breakfast, meditating for 10-15 minutes before work, spending around 45 minutes of playing video games on the Xbox at night, and reading for at least 30 minutes before I go to bed.
The important thing to take away from this post is to build routines and habits that work for your own situation, and which help you achieve goals you set for yourself. If you can find a way to invest in yourself just two hours a day for five days a week - through 48 weeks out of the year - you’ll have spent the equivalent of twelve work weeks (working eight hours a day) on improving yourself.
“Live as if you were to die tomorrow; Learn as if you were to live forever.” - Mahatma Gandhi
As always, thanks again for stopping by to read my pseudo-random musing 😊 While taking some time to rest and reflect here at the end of 2022, you can git checkout other (usually off-topic) content I’m reading over at Instapaper - or read my series on the DevSecOps Essentials as you consider the challenging market dynamics we’re likely to face in 2023.
Until next time, remember to git commit && stay classy!
Cheers,
Keith // securingdev
If you found this post useful or interesting, I invite you to support my content through Patreon 😊 and thanks once again to those who already support this content!😊