DevSecOps Essentials: Talent
TL;DR / Summary at the end of the post. The information shared in this series is the distilled knowledge gained from my experience building the DevSecOps program at Thermo Fisher Scientific (a global Fortune 100 laboratory sciences company).
Full Disclosure up-front: I am employed as a Code Scanning Architect at GitHub at the time of publishing this blog post.
A recap of the DevSecOps Essentials
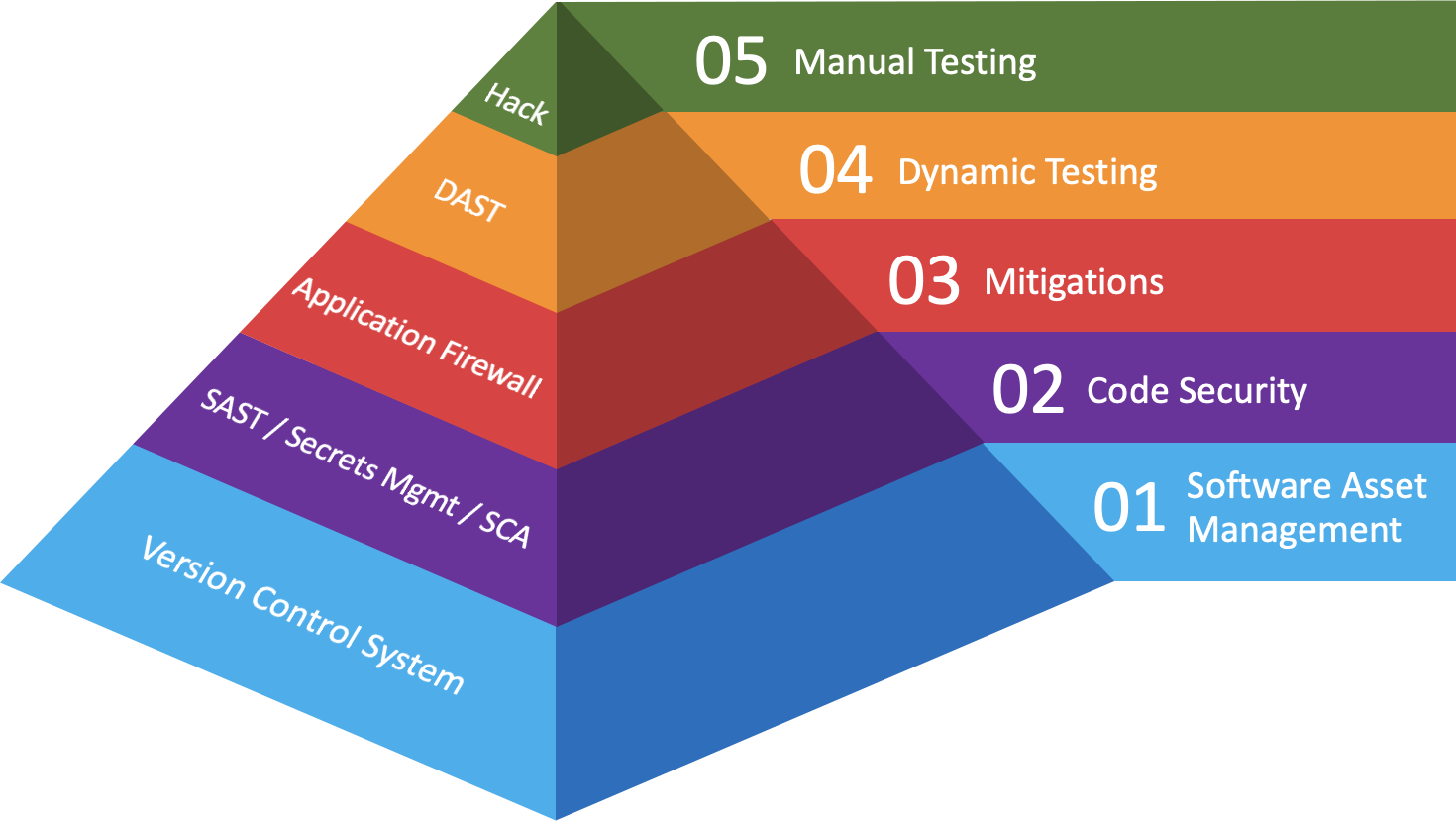
In the first post in this series I gave an overview of what I consider to be the “DevSecOps Essentials”, in terms of both practices and their corresponding technologies.
And while I’ve hinted at it in several posts, there is something missing from the investment categories I’ve drawn out. The one element that cuts across all categories and has the potential to make every investment produce an exponential impact is Talent 🧑💻
Talent comes in many forms, and with the right mix you can create repeatable, scaleable processes to address almost any challenge companies might experience. That being said, before we get started the below diagram recaps how I categorize the technologies companies should investment in so as to maximize the impact of their DevSecOps program:
Background
When I started at Thermo Fisher Scientific I was a team of one. Admittedly it was sort-of odd to be a Manager without anyone reporting to me, but Bryan wanted to bring in a leader who could build out the program from the ground up - and he left it to me to identify the right people to help do that.
As someone who enjoys working remotely, I understand the value in being able to focus on my work without the usual interruptions found in an office setting. As such, I fought for my team members to be hired remotely and to be able to work remotely 🏡. In a field that is historically hard to find talent in, this helped broaden the pool of candidates I could bring onto the team.
Within a year I had brought together an incredible team with diverse talents. Two were hired out of collegiate Computer Science (CompSci) programs 🧑🎓 one came from a Security Research background and had reported a vulnerability to us via coordinated disclosure before applying, another came from the Security industry, one was hired from an internal Software Development team, and unfortunately a really talented person was brought on but had trouble adapting to remote work - and was let go 😞
That last one is still something I feel bad about, because they are an incredibly talented individual who needed more structure than I could offer at that stage in the program’s maturity; I had to learn the hard way that remote work wasn’t for everyone.
Fast forward three years and the two Computer Science graduates have moved on to advanced DevSecOps roles at other companies; The internal hire is now the manager for the Americas team; one of the Security hires is part of the Product Security Research organization, and the other recently became a Director at a security company. Not to mention all of the other great talent who joined the team along the way!
As a leader, I often reflect on how we scaled the program and made our process repeatable - but the thing I’m most proud of is how the people who came to work for me have flourished. In my mind, that is the quintessential representation of a successful DevSecOps program.
The “Talent Shortage” Myth
Dave Kennedy recently published a Twitter thread about the challenges of hiring Information Security talent with the skills his companies need. He had over nine hundred applicants for just two internship roles at his companies. Nine hundred! That doesn’t sound like a shortage to me.
Likewise, Daniel Miessler recently wrote about the fact that finding security talent is largely a function of economics. I agree with his assessment that there exists a dichotomy between large technology companies (🦄) and everyone else when it comes to finding security talent. That being said, I respectfully disagree with some of his conclusions.
When it comes to hiring the best talent, make no mistake that the compensation packages of what Daniel calls the “MANGAcorns” (standing for Meta, Apple, Netflix, Google, Amazon, and so-called “Unicorn” technology companies) will offer the highest values on the market. Nobody else can compete with the revenues these companies are bringing in; therefore nobody else can pay as well.
But these 🦄 companies also have a lot more to lose from a security incident, and appear to understand their return on investment from the security talent they hire. Besides, most companies don’t need the best talent on the market - and most companies don’t have the security maturity to properly utilize the skills that the industry’s best talent can offer.
In an economy increasingly driven by eCommerce transactions, what most companies need are the essentials - with a staff who are curious enough to learn how to leverage them properly, and who are creative enough to scale these technologies to address the company’s risks and threat model(s). Companies don’t need a lot of expensive talent with a wealth of skills and experience to accomplish this.
Aptitude, Attitude, and Engagement
When it comes to working in the field of Information Security, degrees and certifications are - with some exceptions - mostly useless when it comes to the actual work we perform. Don’t get me wrong, for underrepresented groups they will definitely help open doors when it comes to employment. But that doesn’t mean the skills acquired in these programs will be practically applicable.
I myself hold a Bachelor’s Degree in Psychology, and only took continuing education courses in Computer Science. I also identify as a white male who happens to live in America, for which I receive privileges I did not ask for. My experience may be different than yours, and you should do what is best for your situation and experience.
All that being said, the characteristics people need in order to be successful in this industry (and the characteristics that most hiring managers should be looking for) are aptitude, attitude, and engagement.
Note that I didn’t use the word “passion” here; I’m passionate about climate change; I’m passionate about gun safety; I’m passionate about women’s rights; I’m engaged in the field of Information Security. It’s important to understand the difference.
Anyway, people with an aptitude for working with technology are trainable when it comes to most security practices companies need 🧑💻. The ability to take new concepts and translate them to things that are familiar and understandable is a skill that can be applied broadly. It means that people with aptitude pick up on things faster, and can add value quickly.
In order to learn the skills and concepts necessary to be successful, the people hired need to have the right attitude. Empathy, a propensity for seeking out answers, the willingness to ask for help when they need it, and daring to try something (even if they might fail) are all characteristics that show someone has the right attitude in order to add value in a security program.
So how does one measure someone’s aptitude and attitude? Look at how they demonstrate engagement. What are they working on? What are they trying to learn? What areas have they found challenging or interesting? Do they have a home lab? What’s in it? People who are engaged might need a little direction, but can otherwise accomplish all the things the company needs them to.
On the other hand, people that passively went through a university degree or certification program without any engagement have wasted both their time and their money. They will be the ones who don’t have answers to engagement questions, and will expect gainful employment because they hold something that says they received an education 🎓.
You don’t need a degree or a certification to show that you have the right aptitude and attitude to be successful in the field of Information Security. You just need to be able to speak to and/or show what you’re engaged in. The skills and experience will follow.
Training
Hiring people with the right aptitude and attitude - at any skill level - will be a tremendous waste of company resources if we aren’t training them to be ready for the dynamic challenges companies face. Technology is evolving at a rapid clip, and companies are increasing their risk profile by adopting new technologies without consideration for the fact that Security is a Feature.
And while Security trainings are not cheap, consider the old adage of an Executive pushing back on a Manager who’s trying to secure funding for training:
- Executive: “What happens if we invest in training our people and they leave?”
- Manager: “What happens if we don’t, and then they stay?”
I’ll tell you what happens - if they stay, the company has an expensive resource who can secure yesterday’s technologies, but will struggle to reduce the risk profile for all the new technologies the company is adopting. If the company isn’t investing in that person’s growth, either that person stays because they’re not engaged, or leaves because they are engaged and want to keep growing.
On the other hand - if they leave, it probably wasn’t the training that lead them to look elsewhere. People leave bad managers, or they leave companies who put good managers in the position of letting their team down. Likewise, people leave companies that fail to keep pace with the level of compensation their skills warrant, and that fail to acknowledge the outsized impact they have made with the skills they’ve acquired.
If you take care of your people, they will take care of the company. Part of taking care of your people is making sure they are engaged, and the best way to add structure around their engagement is to get them relevant training that they are interested in pursuing.
When to hire Senior Talent
There comes a point in any security program’s maturity where the manager no longer has the capacity to fulfill their responsibilities while also training the team. At this stage it makes sense to bring in senior talent that can help the team level-up, while also expanding the program’s capabilities or shifting in a new direction.
That being said, senior talent also has room for growth - and it’s important to identify what growth that individual is looking for before bringing them onboard. Do they want to build their career as a technologist, or are they looking to shift into management? One resource I highly recommend is “The Manager’s Path” by Camille Fournier to help guide this conversation.
Anyway, my best advice here is this: don’t hire senior talent until there is a problem that requires senior talent to help resolve. Whether that problem is helping the rest of the team level up - or building out a new capability that requires advanced skills - it would be a mistake to bring in expensive talent only to have them grow bored and leave.
How to support this content: If you find this post useful, enjoyable, or influential (and have the coin to spare) - you can support the content I create via Patreon.️ Thank you to those who already support this blog! 😊 And now, back to that content you were enjoying! 🎉
A few words on Leadership
As a leader, I developed a couple of philosophies about how I prioritized my time and attention. On a program level my priorities were as follows:
People > Process > Technology
By focusing on people, I could identify the talent we needed to help us build the process required to scale - and to build relationships with others that we needed to collaborate with. With the right process in place, we could take good technologies and make them great - or take great technologies and make them exponentially more powerful 💥.
As a manager, I defined my primary responsibilities as follows:
- Identify and hire great talent
- Make sure the people we hired were challenged, engaged, and growing
- Obtain the resources the team needed to fulfill our responsibilities
Everything else after that was secondary; without fulfilling these responsibilities, the DevSecOps program at Thermo Fisher Scientific would not have been successful. Moreover, through building a repeatable hiring & talent development process, we could onboard talent at different experience levels and still produce great results.
Again, I highly recommend “The Manager’s Path” by Camille Fournier as required reading for new leaders in a technology field.
The future of DevSecOps
As technology continues to evolve, I foresee greater value being placed on scripting and command-line skills. This is where some university degrees (such as Computer Science) stand out as a baseline for future Information Security talent. My personal recommendations for DevSecOps practitioners would be to learn Python, Bash, and JavaScript.
That being said, having a passing knowledge of modern Web Application Frameworks, Rest APIs, Microservice Architectures, Containers, and SQL can’t hurt. A lot of legacy technologies still run on traditional Web 2.0 infrastructure and likely will continue doing so for many years to come. I don’t expect Function-as-a-Service to be widely adopted for some time, and scripting knowledge will likely help here anyway.
TL;DR / Summary
There’s one investment that can have a multiplicative effect across the other investments in the DevSecOps Essentials, and that will be the talent companies bring into the organization.
While pundits will claim there’s a “talent shortage” in Information Security, I can assure you there most certainly is not. On the other hand, there is definitely a shortage when it comes to understanding what characteristics qualify talent as being capable of doing good work in this industry.
People with the right aptitude, attitude, and engagement have shown time-and-again to be successful in this industry regardless of the skills they entered with. Those with aptitude can be trained; those with the right attitude are equipped to receive that knowledge; and those who are engaged can show the things they are doing to level up their skills.
And the truth is that most organizations don’t need expensive, top-tier talent to improve their security posture. Most companies aren’t nearly mature enough to leverage the skills and experience that top-tier talent could even bring to their organization.
That being said, the future of DevSecOps will demand more programming knowledge as a baseline for new talent to be effective when joining the industry. Those with skills in scripting languages such as Python, Bash, and JavaScript will simply outperform those that without such skills.
Likewise, when considering hiring Senior Talent make sure the company has problems that actually require such skills and experience senior talent brings to the organization. Whether you’ve reached a maturity in your program where the team needs mentorship to continue growing - or you’re adding new capabilities that require experience to do it right - your senior talent will grow bored quickly if you don’t have interesting challenges for them to solve.
Finally, if you’re a leader looking to hire in the field of DevSecOps, my advice would be to lock-in annual budget to get training for the team. The individuals on the team will be the most valuable investment the company can make, as they will shape the processes used to make the technology investments have an impact at scale.
As always, thanks again for stopping by! While I prepare for my next series I’m calling Security Maturity: Teams & Their Technologies, you can git checkout other (usually off-topic) content I’m reading over at Instapaper.
Until next time, remember to git commit && stay classy!
Cheers,
Keith // securingdev
If you found this post useful or interesting, I invite you to support my content through Patreon 😊 and thanks once again to those who already support this content!😊